Introduction
This tutorial provides a comprehensive understanding of User IDs (UIDs) in the Linux operating system. You will learn how to identify the current user's UID, manage user permissions, and control access rights to ensure effective system management and enhanced security.
Understanding User IDs in Linux
In the Linux operating system, every user is associated with a unique identification number called a User ID (UID). This UID is a crucial aspect of user management and access control, as it allows the system to identify and differentiate between different users.
What is a User ID (UID)?
A User ID (UID) is a numerical identifier assigned to each user account on a Linux system. The UID is used by the operating system to keep track of user permissions, file ownership, and other security-related information. The UID range is typically from 0 to 65535, with 0 being reserved for the root user, and the remaining UIDs assigned to regular user accounts.
Understanding UID Ranges
The UID range in Linux is typically divided into the following categories:
- Root User (UID 0): The root user, also known as the superuser, has the highest level of privileges and access to the entire system.
- System Users (UIDs 1-999): These are special user accounts used by the system for various services and processes, such as Apache, MySQL, and SSH.
- Regular Users (UIDs 1000 and above): These are the user accounts created for individual users, and they have varying levels of permissions and access rights.
Identifying the Current User's UID
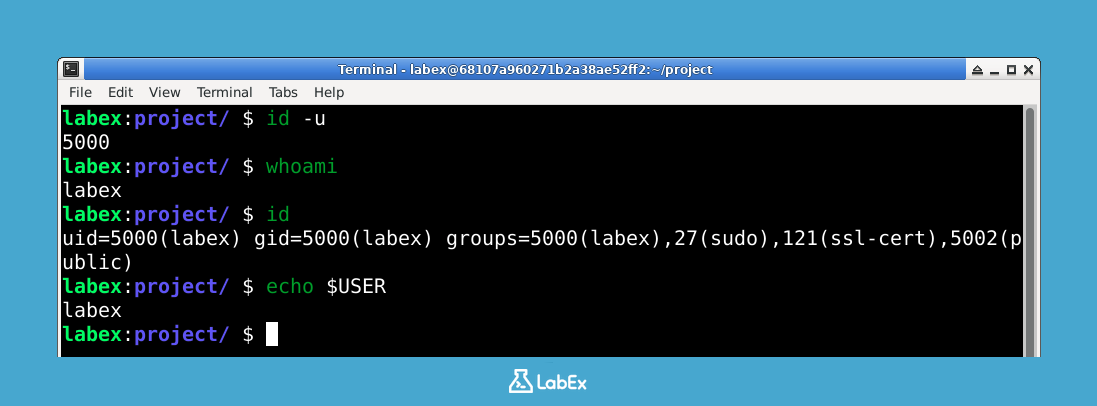
You can easily identify the current user's UID by using the id command in the terminal. Open the terminal and execute the following command:
id -u
You will see output similar to this, showing your current user's UID:
5000

This command will display the UID of the current user, which in this example is 5000.
By understanding the concept of User IDs in Linux, you can effectively manage user accounts, control access, and ensure the security of your system.
Identifying the Current User
Knowing the identity of the current user is essential for managing user permissions and access control in a Linux system. There are several ways to identify the current user, each with its own use case.
Using the whoami Command
The simplest way to identify the current user is by using the whoami command in the terminal. Execute the following command:
whoami
You will see output similar to this, showing your current username:
labex
This command will display the username of the current user, which in this example is "labex".
Using the id Command
Another way to identify the current user is by using the id command. This command provides more detailed information about the user, including the user's UID, primary group ID (GID), and a list of the user's supplementary groups. Execute the following command:
id
You will see output similar to this:
uid=5000(labex) gid=5000(labex) groups=5000(labex),...
The output of the id command shows that the current user has a UID of 5000, a primary GID of 5000, and is a member of several supplementary groups.
Accessing the $USER Environment Variable
You can also access the current user's username through the $USER environment variable. This variable is automatically set by the shell and contains the username of the current user. Execute the following command:
echo $USER
You will see output similar to this:
labex
By using these commands, you can easily identify the current user and gather information about their user account, which is essential for managing user permissions and access control in a Linux system.
Managing User Permissions and Access Control
In Linux, user permissions and access control are crucial for maintaining system security and ensuring that users can only perform authorized actions. The User ID (UID) plays a central role in this process, as it is used to determine the level of access and permissions granted to a user.
Understanding User Permissions
Linux uses a permission system based on three main categories: read, write, and execute. These permissions can be applied to files, directories, and other system resources. The permissions are assigned to three entities: the owner, the group, and others.
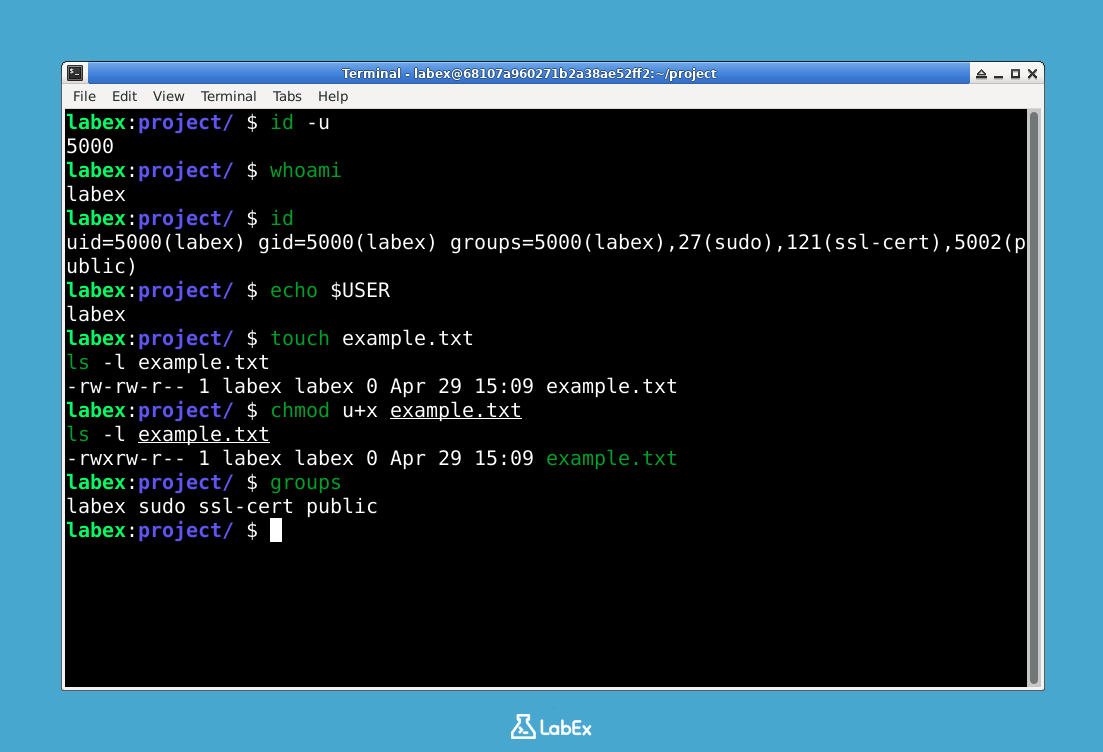
To view the permissions of a file or directory, you can use the ls -l command. Let's create a simple file first. Execute the following commands:
touch example.txt
ls -l example.txt
You will see output similar to this:
-rw-rw-r-- 1 labex labex 0 ... example.txt
In this example, the file "example.txt" is owned by the user "labex" and the group "labex", and the permissions are set to read and write for the owner, read and write for the group, and read-only for others.
Modifying User Permissions
You can use the chmod command to change the permissions of a file or directory. For example, to make the "example.txt" file executable for the owner, you can run the following command:
chmod u+x example.txt
ls -l example.txt
You will see output similar to this, with the execute permission added for the owner:
-rwxrwxr-- 1 labex labex 0 ... example.txt
This will add the execute permission for the owner (user) of the file.
Managing Access Control with Groups
In addition to individual user permissions, Linux also uses groups to manage access control. Users can be assigned to one or more groups, and permissions can be granted to the group as a whole.
To see which groups the current user belongs to, use the groups command:
groups
You will see output similar to this, listing the groups the user is a member of:
labex sudo ssl-cert public
By understanding and managing user permissions and access control, you can ensure that your Linux system is secure and that users can only perform the actions they are authorized to perform.
Summary
In this lab, you have learned about User IDs (UIDs) in Linux and how they are used for user management and access control. You have practiced identifying the current user's UID and username using various commands like id, whoami, and the $USER environment variable. You have also explored basic file permissions using ls -l and learned how to modify them with chmod. Finally, you have seen how groups are used for access control and how to view the groups a user belongs to using the groups command. This knowledge is crucial for system administrators, developers, and anyone working with Linux-based environments.



