Introduction
In this lab, you will learn how to fine-tune Hydra's response wait times when attacking services with potentially slow or unreliable responses. We will use SMTP as an example to demonstrate these concepts.
You will begin by setting up a simple SMTP server with a simulated delayed response using Python. This will allow you to mimic a slow or unreliable network environment. Then, you will run Hydra against this server, first with its default wait time settings, and subsequently adjust the wait time using the -w option to observe its impact. Finally, you will explore the -l and -p options for specifying single credentials directly and test it with a single thread.
Set Up SMTP with Delayed Response
In this step, you will set up a simple SMTP server using Python. This server will introduce a delay in its responses, simulating a slow or unreliable service. This setup is crucial for understanding how Hydra's wait time settings affect its performance.
First, you need to create a Python script named delayed_smtp.py in your ~/project directory. This script will act as your SMTP server.
Open the nano text editor to create this file:
nano ~/project/delayed_smtp.py
Now, copy and paste the following Python code into the delayed_smtp.py file:
import socket
import time
import threading
def handle_client(client_socket):
try:
## Send greeting
client_socket.send(b"220 localhost ESMTP\r\n")
while True:
data = client_socket.recv(1024).decode('utf-8').strip()
if not data:
break
if data.upper().startswith('EHLO') or data.upper().startswith('HELO'):
client_socket.send(b"250-localhost\r\n250-AUTH LOGIN\r\n250 OK\r\n")
elif data.upper().startswith('AUTH LOGIN'):
client_socket.send(b"334 VXNlcm5hbWU6\r\n") ## Username:
client_socket.recv(1024) ## Receive username
## Add 5 second delay
time.sleep(5)
client_socket.send(b"334 UGFzc3dvcmQ6\r\n") ## Password:
client_socket.recv(1024) ## Receive password
client_socket.send(b"235 Authentication successful\r\n")
elif data.upper().startswith('QUIT'):
client_socket.send(b"221 Bye\r\n")
break
else:
client_socket.send(b"250 OK\r\n")
except:
pass
finally:
client_socket.close()
def run_server():
server = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
server.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
server.bind(('127.0.0.1', 1025))
server.listen(5)
print("SMTP server started on port 1025")
while True:
try:
client, addr = server.accept()
thread = threading.Thread(target=handle_client, args=(client,))
thread.daemon = True
thread.start()
except:
break
if __name__ == '__main__':
run_server()
This simplified Python script creates a basic SMTP server that listens on port 1025. The server supports SMTP authentication using the LOGIN method, which is what Hydra expects. The key feature is the time.sleep(5) line in the authentication handler, which introduces a 5-second delay during the authentication process to simulate a slow network response.
After pasting the code, save the file and exit nano by pressing Ctrl + X, then Y, and then Enter.
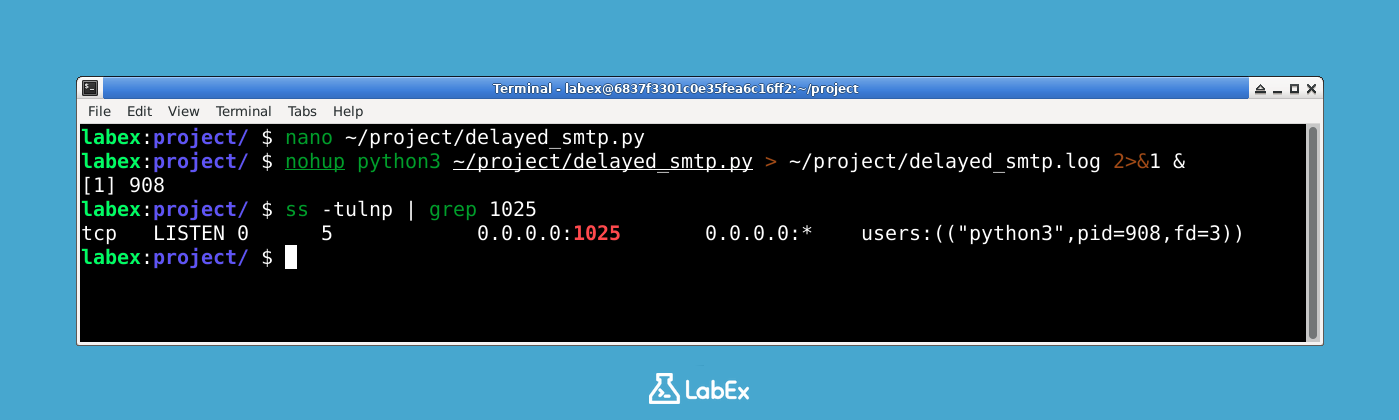
Next, you need to run this Python script in the background. Using nohup ensures that the script continues to run even if you close your terminal session. You will also redirect its output to a log file named delayed_smtp.log for monitoring purposes.
Execute the following command in your terminal:
nohup python3 ~/project/delayed_smtp.py > ~/project/delayed_smtp.log 2>&1 &
This command starts the SMTP server. The & at the end sends the process to the background, allowing you to continue using your terminal.
To confirm that the SMTP server is running and listening on port 1025, you can use the ss command. The ss command is a utility to investigate sockets.
ss -tulnp | grep 1025
You should see output similar to this, indicating that the server is listening on port 1025:
tcp LISTEN 0 4096 0.0.0.0:1025 0.0.0.0:* users:(("python3",pid=XXXX,fd=X))
The pid=XXXX will show the actual process ID of your Python script. This confirms that your delayed SMTP server is now active and ready for testing.
This output confirms that the Python SMTP server is successfully running and listening on port 1025. The LISTEN status indicates the server is ready to accept connections, and the python3 process name confirms our script is running. The 5-second delay built into this server will help us understand how Hydra's wait time settings affect attack performance.
Run Hydra with Default Wait Time
In this step, you will run Hydra against the delayed SMTP server you set up. You will use Hydra's default wait time setting, which is 10 seconds. This will demonstrate how Hydra behaves when the target service has a response delay that is within Hydra's default timeout.
First, you need to create a username list and a password list for Hydra to use. These files will be located in your ~/project directory.
Create the users.txt file:
nano ~/project/users.txt
Add the following usernames to the users.txt file:
testuser
admin
user
Save the file and exit nano (Ctrl + X, Y, Enter).
Next, create the passwords.txt file:
nano ~/project/passwords.txt
Add the following passwords to the passwords.txt file:
password
123456
test
Save the file and exit nano (Ctrl + X, Y, Enter).
Now, you will execute Hydra. You will target the SMTP server running on localhost (127.0.0.1) on port 1025. You will use the smtp module, your users.txt list, and your passwords.txt list. The -t 1 option ensures that Hydra uses only one thread, making the output easier to follow.
hydra -L ~/project/users.txt -P ~/project/passwords.txt -vV -t 1 127.0.0.1 smtp -s 1025
Let's break down the command:
hydra: The command to invoke the Hydra tool.-L ~/project/users.txt: Specifies the path to the file containing the list of usernames.-P ~/project/passwords.txt: Specifies the path to the file containing the list of passwords.-vV: Enables verbose mode, which displays detailed information about the login attempts, including both successful and failed ones.-t 1: Sets the number of parallel tasks (threads) to 1. This is useful for observing each attempt sequentially.127.0.0.1: The target IP address, which is your local machine.smtp: The service module Hydra should use for the attack, in this case, SMTP.-s 1025: Specifies the port number of the target service, which is1025for your delayed SMTP server.
Since your SMTP server has a 5-second delay and Hydra's default wait time is 10 seconds, Hydra should successfully complete each attempt without timing out. You will see output similar to the following, showing Hydra attempting each username and password combination:
labex:project/ $ hydra -L ~/project/users.txt -P ~/project/passwords.txt -vV -t 1 127.0.0.1 smtp -s 1025
Hydra v9.2 (c) 2021 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-05-29 13:47:03
[INFO] several providers have implemented cracking protection, check with a small wordlist first - and stay legal!
[DATA] max 1 task per 1 server, overall 1 task, 9 login tries (l:3/p:3), ~9 tries per task
[DATA] attacking smtp://127.0.0.1:1025/
[VERBOSE] Resolving addresses ... [VERBOSE] resolving done
[ATTEMPT] target 127.0.0.1 - login "testuser" - pass "password" - 1 of 9 [child 0] (0/0)
[VERBOSE] using SMTP LOGIN AUTH mechanism
[1025][smtp] host: 127.0.0.1 login: testuser password: password
[ATTEMPT] target 127.0.0.1 - login "admin" - pass "password" - 4 of 9 [child 0] (0/0)
[VERBOSE] using SMTP LOGIN AUTH mechanism
[1025][smtp] host: 127.0.0.1 login: admin password: password
[ATTEMPT] target 127.0.0.1 - login "user" - pass "password" - 7 of 9 [child 0] (0/0)
[VERBOSE] using SMTP LOGIN AUTH mechanism
[1025][smtp] host: 127.0.0.1 login: user password: password
[STATUS] attack finished for 127.0.0.1 (waiting for children to complete tests)
1 of 1 target successfully completed, 3 valid passwords found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-05-29 13:47:20
This output demonstrates Hydra working with its default 10-second wait time against a server with 5-second delays. Notice that all attempts complete successfully without timeouts, showing that the default wait time is sufficient for this scenario. The [DATA] line shows 9 total attempts (3 users × 3 passwords), and each successful login is marked with [1025][smtp] indicating the port and service type.
Adjust Wait Time with -w
In this step, you will explicitly set Hydra's wait time using the -w option. While the default wait time (10 seconds) was sufficient for our 5-second delay, understanding and controlling this parameter is crucial for adapting Hydra to various network conditions and server behaviors.
You will use the same username and password lists (users.txt and passwords.txt) that you created in the previous step.
Now, execute Hydra again, this time explicitly adding the -w option. This command will behave identically to the previous one, as 10 seconds is Hydra's default wait time, but it demonstrates how to use the option.
hydra -L ~/project/users.txt -P ~/project/passwords.txt -vV -t 1 -w 10 127.0.0.1 smtp -s 1025
Here's the breakdown of the command, with the key difference highlighted:
hydra: The Hydra command.-L ~/project/users.txt: Specifies the username list file.-P ~/project/passwords.txt: Specifies the password list file.-vV: Enables verbose mode.-t 1: Sets the number of threads to 1.-w 10: Explicitly sets the wait time (timeout) to 10 seconds. This means Hydra will wait up to 10 seconds for a response from the target service before considering the attempt a failure.127.0.0.1: The target IP address.smtp: The service module.-s 1025: Specifies the port number.
The output will be similar to the previous step, as the 10-second wait time is sufficient for the 5-second delay of your SMTP server. This step primarily serves to illustrate the usage of the -w option.
Hydra v9.2 (c) 2021 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-05-29 14:02:49
[INFO] several providers have implemented cracking protection, check with a small wordlist first - and stay legal!
[DATA] max 1 task per 1 server, overall 1 task, 9 login tries (l:3/p:3), ~9 tries per task
[DATA] attacking smtp://127.0.0.1:1025/
[VERBOSE] Resolving addresses ... [VERBOSE] resolving done
[ATTEMPT] target 127.0.0.1 - login "testuser" - pass "password" - 1 of 9 [child 0] (0/0)
[VERBOSE] using SMTP LOGIN AUTH mechanism
[1025][smtp] host: 127.0.0.1 login: testuser password: password
[ATTEMPT] target 127.0.0.1 - login "admin" - pass "password" - 4 of 9 [child 0] (0/0)
[VERBOSE] using SMTP LOGIN AUTH mechanism
[1025][smtp] host: 127.0.0.1 login: admin password: password
[ATTEMPT] target 127.0.0.1 - login "user" - pass "password" - 7 of 9 [child 0] (0/0)
[VERBOSE] using SMTP LOGIN AUTH mechanism
[1025][smtp] host: 127.0.0.1 login: user password: password
[STATUS] attack finished for 127.0.0.1 (waiting for children to complete tests)
1 of 1 target successfully completed, 3 valid passwords found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-05-29 14:03:05
This output demonstrates the explicit use of -w 10 to set the wait time to 10 seconds, producing identical results to the default setting. The attack completed successfully, finding all 3 valid passwords within the 16-second timeframe (14:02:49 to 14:03:05). This step shows how you can explicitly control timeout settings, which becomes essential when dealing with servers that have response times longer than the default 10-second limit.
Test Single Credential with -l and -p Options
In this step, you will learn how to use Hydra's -l and -p options to test a single username and password combination. This approach allows you to specify a single credential pair directly on the command line, rather than using separate files. This is particularly useful for quickly testing a specific credential pair without creating or modifying files.
You will continue to use the delayed SMTP server you set up in the first step.
Execute the following Hydra command, using the -l option to specify the username and -p option to specify the password:
hydra -t 1 -l testuser -p password -vV 127.0.0.1 smtp -s 1025
Let's break down this command:
hydra: The Hydra command.-t 1: Sets the number of threads to 1, ensuring a clear, sequential attempt.-l testuser: Specifies the username to test. The-l(lowercase L) option is used for a single username.-p password: Specifies the password to test. The-poption is used for a single password.-vV: Enables verbose mode.127.0.0.1: The target IP address.smtp: The service module.-s 1025: Specifies the port number.
In this scenario, Hydra will only attempt to log in with the single credential pair testuser:password. Since our SMTP server accepts any credentials for demonstration purposes, Hydra will report a successful login.
You will see output similar to this:
labex:project/ $ hydra -t 1 -l testuser -p password -vV 127.0.0.1 smtp -s 1025
Hydra v9.2 (c) 2021 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-05-29 13:50:25
[INFO] several providers have implemented cracking protection, check with a small wordlist first - and stay legal!
[DATA] max 1 task per 1 server, overall 1 task, 1 login try (l:1/p:1), ~1 try per task
[DATA] attacking smtp://127.0.0.1:1025/
[VERBOSE] Resolving addresses ... [VERBOSE] resolving done
[ATTEMPT] target 127.0.0.1 - login "testuser" - pass "password" - 1 of 1 [child 0] (0/0)
[VERBOSE] using SMTP LOGIN AUTH mechanism
[1025][smtp] host: 127.0.0.1 login: testuser password: password
[STATUS] attack finished for 127.0.0.1 (waiting for children to complete tests)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-05-29 13:50:30
This output demonstrates testing a single credential pair using -l and -p options instead of wordlist files. Notice the [DATA] line now shows 1 login try (l:1/p:1), indicating only one username and one password are being tested. This approach is efficient for targeted testing when you have specific credentials to verify, and it completes much faster since there's only one attempt instead of nine.
Summary
In this lab, you have learned how to fine-tune Hydra's behavior when dealing with services that have slow or unreliable responses.
You started by setting up a simulated slow SMTP server using a Python script, which introduced a 5-second delay in its responses. This allowed you to create a controlled environment to test Hydra's timeout settings. You then ran Hydra against this server, first observing its default behavior, and then explicitly adjusted the wait time using the -w option. Finally, you explored the -l and -p options for specifying single credentials directly on the command line, which is useful for quick, targeted tests.
This lab has provided you with practical experience in configuring Hydra for various network conditions, enhancing your ability to perform effective brute-force attacks.


