Introduction
In this lab, you'll learn how to use the Linux ssh command to remotely connect to and manage other Linux systems. SSH (Secure Shell) is a powerful tool for system administrators and network engineers, allowing you to perform a wide range of tasks remotely and securely.
Achievements
By the end of this lab, you'll be able to:
- Use the
sshcommand to connect to a remote system securely - Execute commands on a remote system using SSH
- Understand the basics of remote system management
Retrieve the labex User Password
Before we can use SSH, we need to know the password for the labex user. In this lab environment, the password is stored as an environment variable.
- Open a terminal window in the desktop environment, only the desktop environment terminal will have the environment variables set.
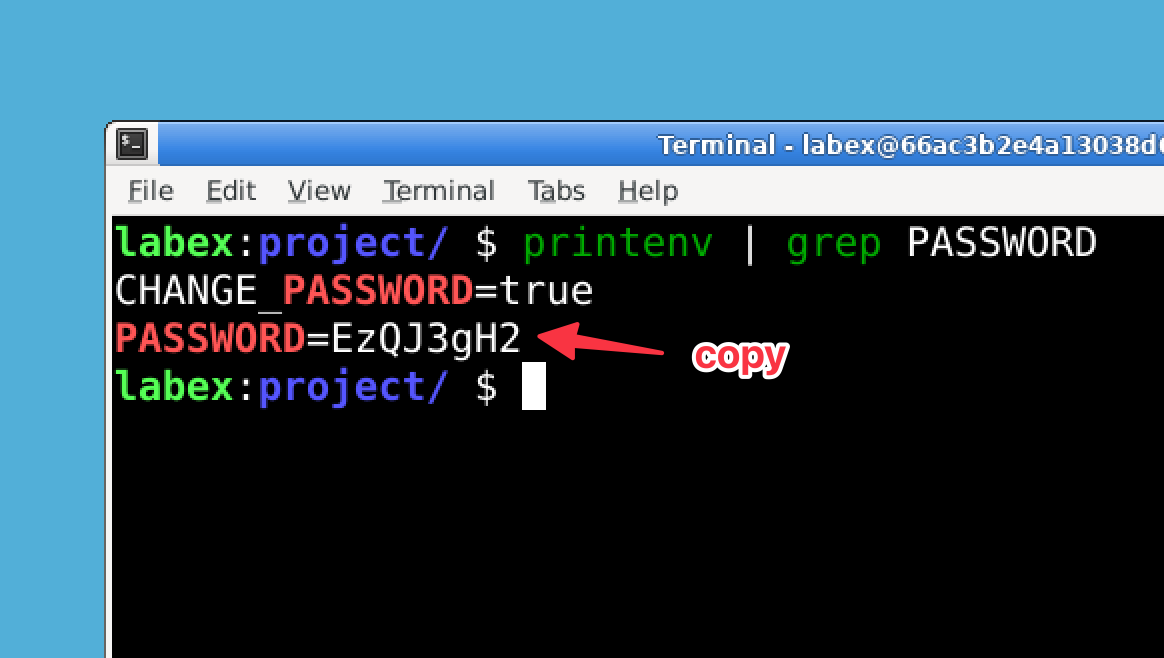
To retrieve the password, run the following command.
printenv | grep PASSWORDNote: You must run this command in the desktop environment terminal, not in the terminal that you opened from the top menu bar.
This command will display all environment variables containing "PASSWORD". Look for a line that says
LABEX_PASSWORD=.... The characters after the equals sign are your password.Make a note of this password, as you'll need it for the subsequent steps.
Important: Do not attempt to change the labex user password. The lab environment is set up with this specific password, and changing it may cause the lab verification steps to fail. Always use the password provided by the LABEX_PASSWORD environment variable throughout this lab.
Connect to the Local System Using SSH
Now that we have the password, let's practice using SSH to connect to the local system. This simulates connecting to a remote system.
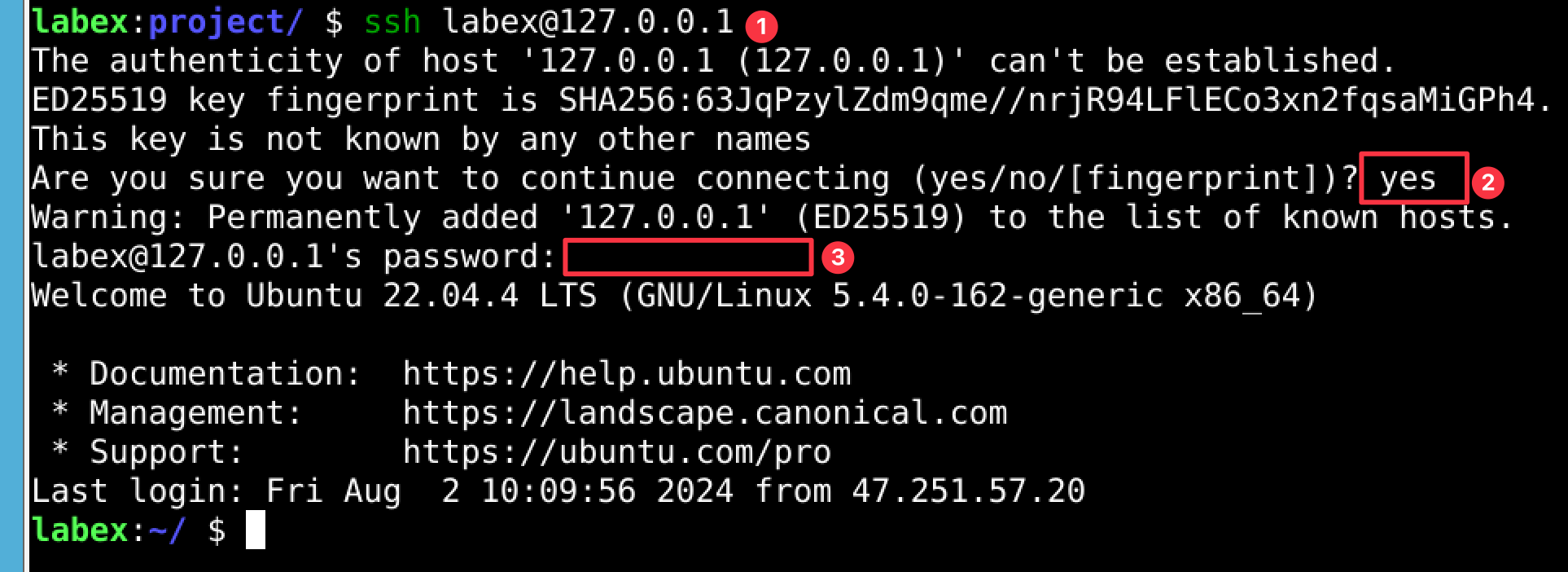
In the terminal, use the following command to connect to the local system using SSH:
ssh labex@127.0.0.1Here,
127.0.0.1is the loopback IP address that refers to the local machine. It's often called "localhost".You may see a message about the authenticity of the host. This message appears because it's the first time you're connecting to this "remote" system. In a real-world scenario, you should verify the fingerprint before proceeding. For this lab, type
yesand press Enter to continue.When prompted for a password, enter the password you retrieved in Step 1. You won't see the password as you type it.
If successful, you'll see a new prompt. This indicates you're now connected via SSH, even though you're still on the same machine.
To exit the SSH session, type
exitand press Enter. This will return you to your original terminal session.
Execute a Simple Command Using SSH
Let's practice executing a command on the "remote" system using SSH. This is useful when you need to run a quick command without starting a full SSH session.
Use the following command to list the contents of the home directory on the local system via SSH:
ssh labex@127.0.0.1 'ls -l ~'This command breaks down as follows:
ssh: The command to start an SSH connectionlabex@127.0.0.1: The user and IP address we're connecting to'ls -l ~': The command we want to run on the remote system, enclosed in quotes
Enter the
labexuser password when prompted.You should see the output of the
ls -l ~command, showing the contents of the home directory. This output is coming from the "remote" system, even though it's actually the same machine.Notice how you didn't enter a full SSH session this time. The command was executed, and you were immediately returned to your original terminal.
Use SSH with Pseudo-Terminal Allocation
Some commands require a pseudo-terminal for proper execution, especially interactive commands or those that produce formatted output. Let's practice using the -t option with SSH to force pseudo-terminal allocation.
Run the following command to view the system's uptime:
ssh -t labex@127.0.0.1 'uptime'The
-toption forces SSH to allocate a pseudo-terminal. This can be necessary for commands that expect to be run in an interactive environment.Enter the
labexuser password when prompted.You should see output showing how long the system has been running, along with load average information.
Now, let's try an interactive command. Run the following:
ssh -t labex@127.0.0.1 'top -n 1'This will run the
topcommand, which usually provides an interactive view of system processes, but here we're using the-n 1option to exit after one iteration.Again, enter the
labexuser password when prompted.You should see a formatted output showing the top processes running on the system.
Create and Access a Remote File
Let's practice creating a file on the "remote" system and accessing it. This demonstrates how you can manipulate files on a remote system using SSH.
Use SSH to create a file named
remote_test.txtin the home directory of the remote system:ssh labex@127.0.0.1 'echo "This is a test file created remotely" > ~/remote_test.txt'This command uses SSH to run an
echocommand on the remote system, which then outputs text into a new file.Now, let's view the contents of the file we just created:
ssh labex@127.0.0.1 'cat ~/remote_test.txt'The
catcommand is used to display the contents of the file.You should see the message "This is a test file created remotely" displayed in your terminal.
Let's confirm the file's presence by listing it:
ssh labex@127.0.0.1 'ls -l ~/remote_test.txt'This will show you the file details, including permissions, size, and creation date.
Summary
In this lab, you've learned how to use the ssh command to remotely connect to and manage Linux systems. You've practiced retrieving a user password from environment variables, connecting to a local system via SSH (simulating a remote connection), executing commands remotely, using SSH with pseudo-terminal allocation, and creating and accessing files on a "remote" system.
These skills are fundamental for system administrators and anyone who needs to manage Linux systems remotely. Remember, while we used the local system for practice, these same commands and techniques can be used to connect to and manage truly remote systems across a network or the internet.
Always prioritize security when working with remote systems. Use strong passwords, keep your systems updated, and consider additional security measures like key-based authentication for production environments.
As you continue your journey in system administration, you'll find SSH to be an indispensable tool for remote management and troubleshooting.



