Introduction
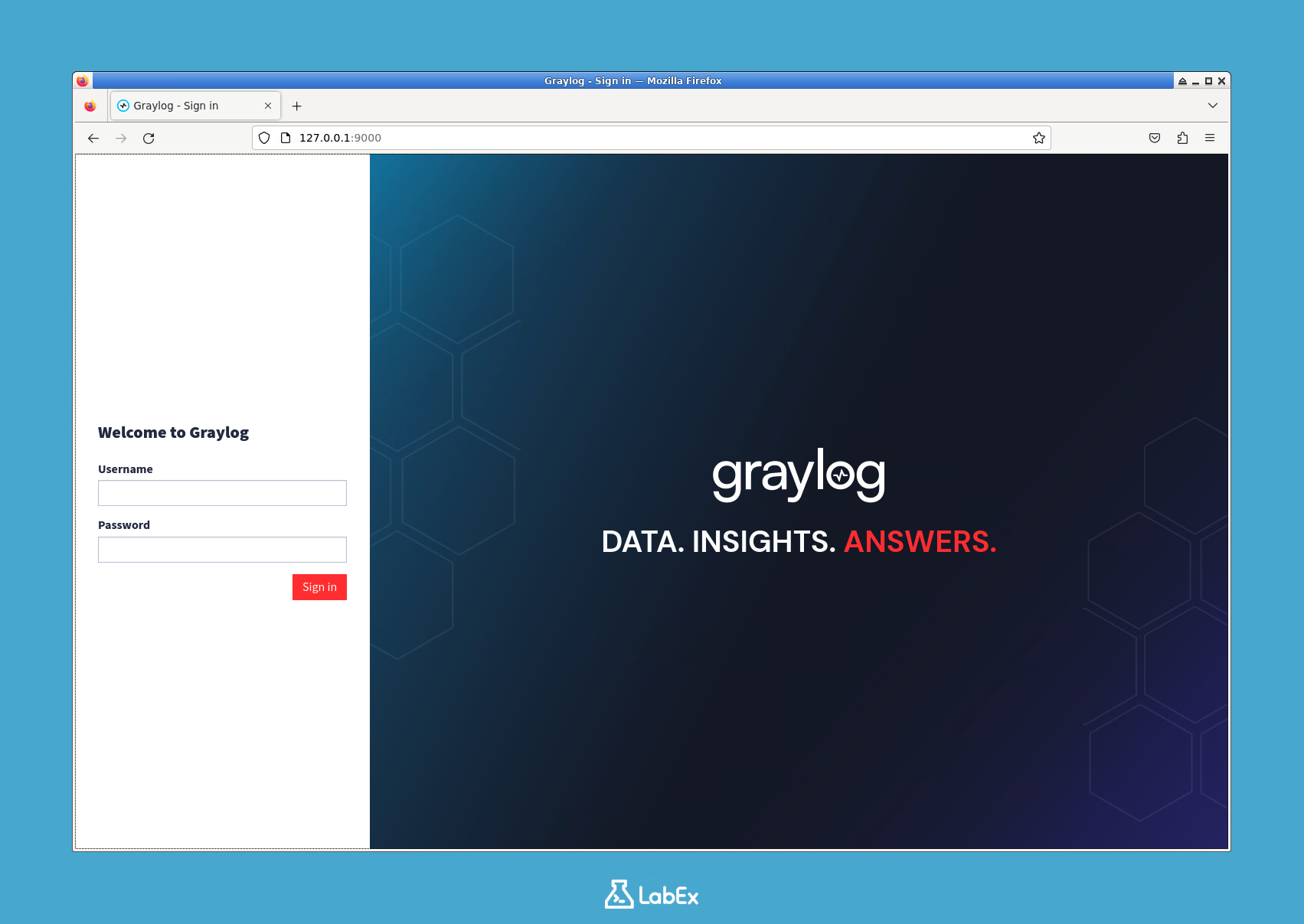
In this lab, you will learn how to use Graylog, a powerful open-source log management platform, for collecting and analyzing log data. Centralized logging is a critical component of cybersecurity, allowing you to monitor system events, detect anomalies, and investigate security incidents from a single interface.
You will start by deploying the entire Graylog stack, which includes MongoDB and OpenSearch (the modern replacement for Elasticsearch), using Docker Compose. You will then configure Graylog to receive log data, send sample logs to it, perform search queries to filter information, and finally, build a visual dashboard to monitor key metrics. By the end of this lab, you will have hands-on experience with the fundamental workflow of log analysis in Graylog.