はじめに
この実験では、強力なネットワークログインクラッカーである Hydra を使用して、追加のパスワードチェックを行う方法を学びます。具体的には、LabEx VM 上に Telnet サービスを設定し、Hydra に -e nsr オプションを使用してパスワードクラッキングを試みます。このオプションを使用すると、Hydra は自動的に null パスワード、ユーザー名そのものをパスワード、およびユーザー名の逆順をパスワードとして試します。これは、ペネトレーションテストで、弱いまたはデフォルトの認証情報を迅速に特定するために使用される一般的な手法です。
この実験では、LabEx VM 上の Telnet サービスのインストールと設定手順を案内します。その後、Hydra の -e nsr フラグを使用して、これらの追加のチェックが単純なパスワードを見つけるためにどのように使用できるかを示します。最後に、-e ns オプションのみを使用した場合の結果と比較することで、逆順のユーザー名チェックを含めることの影響を理解します。
Telnet サービスの設定
このステップでは、LabEx VM 上に Telnet サービスを設定します。Telnet は、リモートサーバーへのコマンドラインインタフェースを提供するネットワークプロトコルです。Telnet は一般的に本番環境では、データが平文で送信されるため、安全とは言えませんが、制御された実験環境でパスワードクラッキング手法をデモするために適しています。
最初に、null パスワードを持つテストユーザーアカウントを作成する必要があります。
sudo useradd -m testuser
sudo passwd -d testuser
passwd -d コマンドは、ユーザーのパスワードを削除し、実質的に null パスワードを作成します。
Telnet の設定ファイル /etc/inetd.conf を編集する必要があります。nano エディタを使用してこのファイルを開きます。
sudo nano /etc/inetd.conf
nano エディタ内で、telnet で始まる行を探します。次のようになっているはずです。
telnet stream tcp nowait telnetd /usr/sbin/tcpd /usr/sbin/telnetd
この行の先頭に # を付けてコメントアウトします。
#telnet stream tcp nowait telnetd /usr/sbin/tcpd /usr/sbin/telnetd
次に、コメントアウトされた行の下に次の行を追加します。この新しい行は、認証を無効にする -i オプションを使用して Telnet を設定します。
telnet stream tcp nowait telnetd /usr/sbin/in.telnetd -i
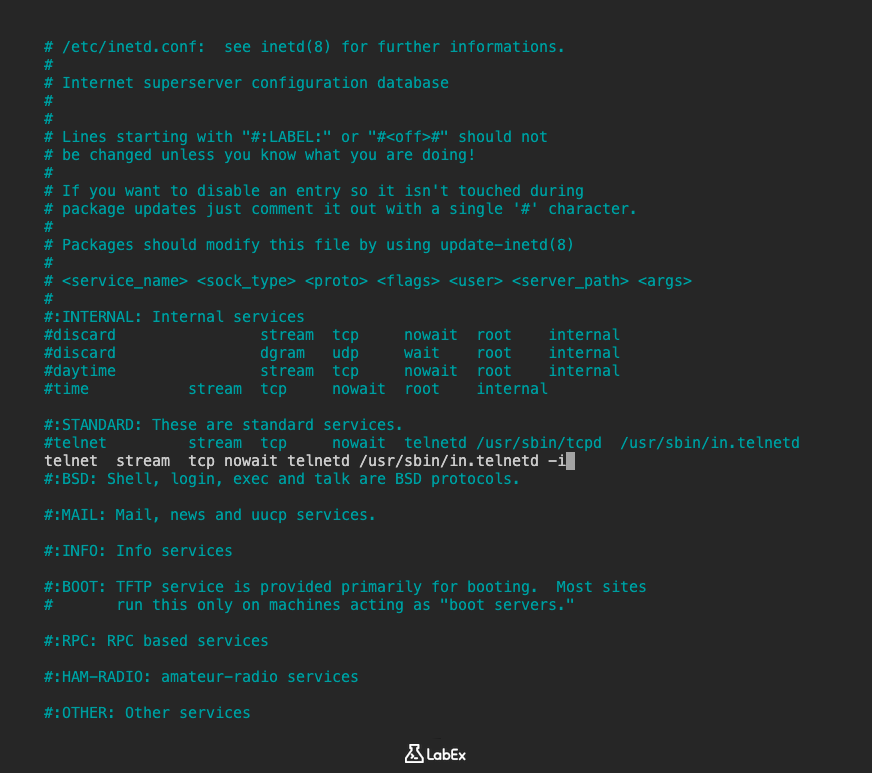
/etc/inetd.conf ファイルの該当する部分は、次のようになります。
#telnet stream tcp nowait telnetd /usr/sbin/tcpd /usr/sbin/telnetd
telnet stream tcp nowait telnetd /usr/sbin/in.telnetd -i
nano を終了するには Ctrl+X を押します。保存を促されたら、Y を押して Enter キーを押して /etc/inetd.conf に変更を保存します。
さらに、PAM が Telnet の null パスワードを許可するように設定されていることを確認する必要があります。PAM 設定を確認します。
cat /etc/pam.d/common-auth | grep pam_unix.so
次の様な行が表示されるはずです。
auth [success=1 default=ignore] pam_unix.so nullok
この行に nullok が含まれていない場合は、追加する必要があります。ファイル編集します。
sudo nano /etc/pam.d/common-auth
pam_unix.so を含む行を探し、既に存在しない場合は末尾に nullok を追加します。変更があればファイルを保存して終了します。
最後に、変更が有効になるように inetd サービスを再起動する必要があります。Docker コンテナ環境にいるため、/etc/init.d スクリプトを使用してサービスを再起動します。
sudo /etc/init.d/openbsd-inetd restart
サービスの再起動を示す出力が表示されます。
* Restarting internet superserver inetd
これで、この実験のためにパスワードなしでログインを許可するように、Telnet サービスが設定されました。
Hydra を -e nsr チェックで実行する
このステップでは、Hydra を使用して Telnet サービスに対してブルートフォース攻撃を実行します。特に -e nsr オプションを使用して、Hydra に null パスワード、ユーザー名自体、およびユーザー名の逆順を潜在的なパスワードとして試させるように指示します。
~/project ディレクトリでターミナルを開き、以下のコマンドを実行します。
hydra -l testuser -P ~/project/unix_passwords.txt -vV -e nsr telnet://localhost
このコマンドを分解してみましょう。
hydra: Hydra ツールを実行するコマンドです。-l testuser: 攻撃に使用するユーザー名を指定します。null パスワードを持つ、作成したテストユーザーを対象とします。-P ~/project/unix_passwords.txt:-eで指定されたチェックに加えて使用するパスワードリストファイルです。このファイルには、設定ステップでダウンロードした一般的な Unix パスワードのリストが含まれています。-vV: 詳細な出力を有効にし、各ログイン試行とその結果を表示します。-e nsr: このステップの重要なオプションです。Hydra に追加のチェックを実行するように指示します。n: null パスワード(空の文字列)を試します。s: ユーザー名 (testuser) をパスワードとして試します。r: ユーザー名の逆順 (resutest) をパスワードとして試します。
telnet://localhost: ターゲットサービスとアドレスを指定します。telnetは Telnet プロトコルを示し、localhostはローカルマシン(LabEx VM 自体)を示します。
コマンドを実行します。Hydra は、指定されたユーザー名とリストのパスワード、null パスワード、ユーザー名、およびユーザー名の逆順を使用して、ポート 23(デフォルトの Telnet ポート)の Telnet サービスにログインしようとします。
Hydra が試行を行う際に、次の様な出力が表示されます。
Hydra vX.Y (c) 2020 by van Hauser/THC - use allowed only for legal purposes.
Hydra is starting...
[DATA] 1 task, 1 server, XXXX service(s)
[DATA] attacking service telnet on port 23
[DATA] attacking target localhost
[ATTEMPT] target localhost - login: 'testuser' - pass: ''
[23][telnet] host: localhost login: testuser password:
[ATTEMPT] target localhost - login: 'testuser' - pass: 'testuser'
[ATTEMPT] target localhost - login: 'testuser' - pass: 'resutest'
...
テストユーザーが null パスワードを持つように設定されているため、Hydra は null パスワード(空のパスワードを使用した最初の試行)を使用してすぐにログインに成功するはずです。
正常実行の確認
In this step, we will examine the output from the Hydra command you just ran to identify the successful login attempts.
Scroll back through the output in your terminal. Look for lines that indicate a successful login. These lines are typically marked with the port number and service, followed by the host, login, and password.
Since we configured the Telnet service to allow logins without a password, you should see a line similar to this in the output:
[23][telnet] host: localhost login: testuser password:
This line confirms that Hydra successfully logged in to the Telnet service on localhost using the username testuser and a null password (indicated by the empty space after password:).
You might also see other successful logins if any of the passwords in the ~/project/unix_passwords.txt file match the actual password for the testuser user (although in this lab setup, the null password is the intended successful check).
The -vV option provides detailed output for each attempt, which is useful for understanding how Hydra is progressing and which passwords it is trying. The successful login line clearly shows the credentials that worked.
This step demonstrates how the -e nsr option helps in quickly identifying common weak password scenarios, such as null passwords, which are often overlooked in standard password lists.
-e ns チェックとの比較
このステップでは、Hydra を再び実行しますが、今回は -e ns オプションを -e nsr の代わりに使用します。これにより、Hydra に null パスワードとユーザー名をパスワードとして試させるように指示しますが、ユーザー名の逆順を試させることはありません。このコマンドの出力を前のコマンドの出力を比較することで、実行されたチェックの違いを確認できます。
~/project ディレクトリでターミナルを開き、以下のコマンドを実行します。
hydra -l testuser -P ~/project/unix_passwords.txt -vV -e ns telnet://localhost
このコマンドは前のコマンドとほぼ同じで、唯一の違いは -e ns オプションです。
-e ns: このオプションは、Hydra に以下の追加チェックを実行するように指示します。n: null パスワードを試します。s: ユーザー名 (testuser) をパスワードとして試します。
コマンドを実行します。Hydra は再び Telnet サービスにログインを試み、リストのパスワード、null パスワード、およびユーザー名をパスワードとして試します。
出力を確認します。前の実行と同様に、null パスワードとユーザー名をパスワードとして試す試行が表示されます。ただし、ユーザー名の逆順 (resutest) の試行は表示されません。
Hydra vX.Y (c) 2020 by van Hauser/THC - use allowed only for legal purposes.
Hydra is starting...
[DATA] 1 task, 1 server, XXXX service(s)
[DATA] attacking service telnet on port 23
[DATA] attacking target localhost
[ATTEMPT] target localhost - login: 'testuser' - pass: ''
[23][telnet] host: localhost login: testuser password:
[ATTEMPT] target localhost - login: 'testuser' - pass: 'testuser'
...
このコマンドの出力をステップ 2 の出力と比較することで、-e nsr オプションにはユーザー名の逆順チェックが含まれているのに対し、-e ns オプションには含まれていないことが明確になります。これは、Hydra のさまざまなオプションを使用してパスワードクラッキングプロセスをカスタマイズし、特定のシナリオで関連する特定の種類のチェックを含めることができることを示しています。
まとめ
この実験では、LabEx 仮想マシン上に Telnet サービスを設定し、-e nsr オプションを使用することで、Hydra で追加のパスワードチェックを行う方法を学びました。telnetd パッケージをインストールし、/etc/inetd.conf ファイルを変更し、PAM を設定することで、null パスワードを許可するように Telnet サービスを設定しました。これは、null パスワードを持つテストユーザーを作成することで実現しました。
その後、-e nsr オプション付きの Hydra を使用してパスワードクラッキングを試行しました。これは、null パスワード、ユーザー名、およびユーザー名の逆順をパスワードとして試すことを含みます。出力を観察し、null パスワードを使用した成功したログインを特定しました。最後に、-e ns オプションを使用した結果と比較することで、実行されたチェックの違いを理解しました。この実験は、Hydra の追加のパスワードチェックが、一般的な弱い認証情報を迅速に特定するためにどのように使用できるかを示しました。